What were the main scientific goals of the project?
In the Hexa-X-II project, we investigated security and data protection aspects at chip level – i.e. in the hardware, software and operating systems of 6G mobile devices. The central challenge is to develop a design that is trustworthy and at the same time meets high performance and energy efficiency requirements.
What results or findings have emerged from the project?
A total of three Barkhausen Institute research groups were involved in the project, each with a different specialist focus.
In the Scalable Computing Hardware research group, we developed a trustworthy chip architecture that addresses the security requirements of 6G devices at hardware, software and operating system level. On this basis, a new concept for integrating hardware accelerators was proposed to meet the performance and resource requirements of applications in 6G mobile devices.
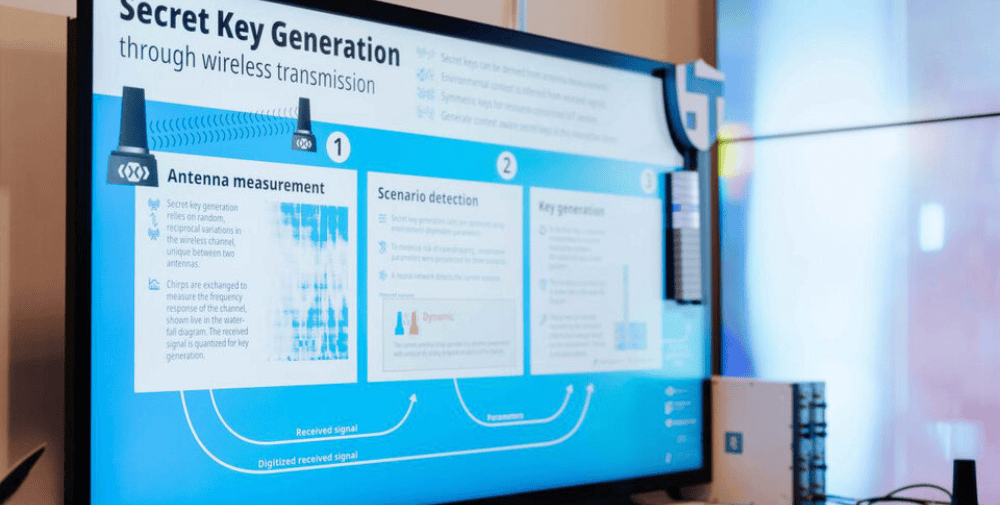
The Wireless Connectivity and Sensing research group developed a demonstrator for context-aware secret key generation for secure device-to-device communication. The received radio signals are influenced by the physical properties of the environment, such as reflection or scattering. These signals can be converted into secure bit sequences on both devices, which can then be used for encryption. The demonstrator shows how two devices exchange signals, capture environmental contexts and generate secret bits from them, which are visualized in the form of a physical key.
The Trustworthy Data Processing research group focused on data protection and security aspects of the upcoming radar sensing functionalities in 6G systems. To this end, a comprehensive threat analysis was carried out and, based on this, a countermeasure was developed to reduce security and data protection risks in connection with radar sensing.
What happens to the research results?
The results were published at scientific conferences and in project reports. Since the work has primarily presented initial concepts for secure chip architectures, we will continue to pursue the topic in follow-up projects to further increase the trustworthiness of 6G devices.
Are the results available as open source for the scientific community?
Yes. Our general secure chip architecture including the operating system has been published as open source on GitHub:
https://github.com/Barkhausen-Institut/M3
https://github.com/Barkhausen-Institut/M3-hardware
How do citizens, companies or other institutions benefit from the project results?
The further development of 6G mobile networks will enable more and more functions in intelligent systems and communication devices that influence our everyday lives and decision-making processes. Their reliability is therefore crucial. Failures of such systems can not only impair functionality, but also pose risks to human safety. This is why research that addresses vulnerabilities and strengthens the trustworthiness of future 6G devices is important.
What does the project mean for you and your research personally?
At the Barkhausen Institute, we are researching the trustworthiness of networked electronic systems. As Hexa-X-II focuses specifically on 6G mobile networks, we had the special opportunity to apply our research concepts to upcoming 6G devices and their specific requirements. The exchange with project partners who bring in application-level expertise helps us to expand our know-how and further develop our research directions.
– – – – – –
Further links
👉 www.barkhauseninstitut.org
Photo: 5G Lab / Marcus Hartelt